San Francisco, NFAPost: After ZuoRAT and HiatusRAT over the past year, a new third malware strain AVrecon has been found covertly targeting small office/home office (SOHO) routers, infiltrating over 70,000 devices and creating a botnet with 40,000 nodes spanning 20 countries.
Lumen Black Lotus Labs has warned its spread across the globe. A majority of the infections are located in the U.K. and the US, followed by Argentina, Nigeria, Brazil, Italy, Bangladesh, Vietnam, India, Russia, and South Africa, among others.
Expressing its view on the development, SOHO states that this makes AVrecon one of the largest SOHO router-targeting botnets ever seen.
“The purpose of the campaign appears to be the creation of a covert network to quietly enable a range of criminal activities from password spraying to digital advertising fraud,” states SOHO.
According to sources, AVrecon malware was first highlighted by Kaspersky senior security researcher Ye (Seth) Jin in May 2021, indicating that the malware has managed to avoid detection until now.
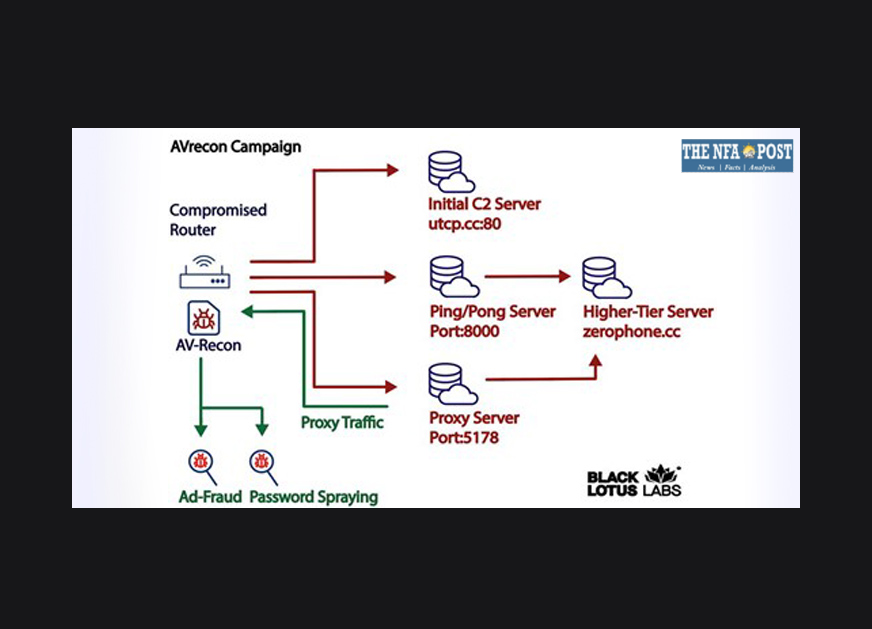
As per the attack chain detailed by Lumen, a successful infection is followed by enumerating the victim’s SOHO router and exfiltrating that information back to an embedded command-and-control (C2) server.
“It also checks if other instances of malware are already running on the host by searching for existing processes on port 48102 and opening a listener on that port. A process bound to that port is terminated,” states Lumen.
The next stage involves the compromised system establishing contact with a separate server, called the secondary C2 server, to await further commands. Lumen said it identified 15 such unique servers that have been active since at least October 2021.
It is interesting to note that tiered C2 infrastructure is prevalent among notorious botnets like Emotet and QakBot.
Since AVrecon is written in the C programming language, it is easy to port the malware for different architectures. It is noted that the malware leverage infrastructure living on the edge that typically lacks support for security solutions and spread very fast.
According to various evidence, the botnet used for clicking on various Facebook and Google ads and to interact with Microsoft Outlook helps in its spread. This likely indicates a two-pronged effort to conduct advertising fraud and data exfiltration.
“The manner of attack seems to focus predominantly on stealing bandwidth – without impacting end-users – in order to create a residential proxy service to help launder malicious activity and avoid attracting the same level of attention from Tor-hidden services or commercially available VPN services,” the researchers said.